|
||
|
May 9, 2012 - Vol 2, Issue 8 |
||
|
||



|

Forensic Analysis using QAUDJRN Part 2

By Dan Riehl In this second installment of the series dealing with forensic analysis by using the QAUDJRN journal, the focus is on the forensic analysis of user activity. I discuss how to audit and report on various activities performed by a particular user, and I also show how to audit and report on security-related events caused by all users. As examples, I examine how to audit and report on every time QSECOFR changes a system value, and I also discuss how to audit and report on every occurrence in which any user deletes any object. Auditing RevisitedI encourage you to review the previous article in this series (" Forensic Analysis Using QAUDJRN, Part 1: CL Command Usage" from the February 1, 2012 Issue of the SecureMyi Security Newsletter), which discusses the basics of auditing and reporting from the system security audit journal QAUDJRN. In order to begin reporting on security related activities, you must first configure your system to perform the auditing functions you need. The system values QAUDCTL and QAUDLVL must be set for your desired level of auditing, and the QAUDJRN journal must have been created on your system. Every security-related event that occurs on your system is tied to a particular user. In this article, the focus is on reporting on the activities performed by a user. Usually, we want to report on the activities of our powerful users such as QSECOFR and system administrator users. Powerful IT users and other users with command-line access have the freedom to navigate the system outside of the constraints of a menu system that would otherwise confine their activities to those allowed by their menu options. Having said that, let me also say that you can audit and report on the activities of any user, regardless of the user's power or ability to navigate the system. When you want to be able to audit and report on the activities of a particular user, you must first decide which events you're interested in collecting. If you don't care whether someone moves a spooled file report from one output queue to another, or if you don't care when a program adopts authority, it affects your choices when configuring auditing. If you want to be able to track each time a new library is created on the system or every time a file is deleted, it likewise affects your auditing configuration. The events that can be audited are described by a combination of the allowable values for the system values QAUDLVL and QAUDLVL2, and the allowable values for the AUDLVL attribute of each user profile. |
|
In This Issue
Feature Article - Forensic Analysis with QAUDJRN - Tracing User Activity Security Quick Links
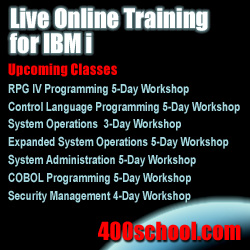
Please Visit Our Sponsors
Platinum Sponsor |
IBM i Security and Audit ResourcesIBM i Security Videos from SecureMyi.com SecureMyi Newsletter Home and ArchivesIBM i Security Reference - IBM i 6.1 IBM i Security Reference - IBM i 7.1 QAUDJRN Audit Types By AUDLVL 6.1 QAUDJRN Entry Type Record Layout 6.1 RedBook - Security Guide for IBM i 6.1 PCI SSC Data Security Standards 


|

|
Featured YouTube Educational VideoIBM i Security

|
||
IBM i Security News Bytes
Cilasoft Introduces "Elevated Authority Manager" For IBM i
Raz-Lee Launches into the Database Universe with Revolutionary "DB-Gate"
Arpeggio Software releases new Version of SIFT-IT Free Edition
New Book - Now Shipping - IBM i Security Administration and Compliance
Free - New White Paper "How Much Security is Enough?" IBM i Security Calendar of Events
|



|
|
|
||
Security Shorts

Alternative to Extracting and Formatting QAUDJRNBy Dan Riehl In the above Feature Article "Forensic Analysis using QAUDJRN Part 2". I explain how you can extract information from the system QAUDJRN audit journal to provide a formatted output file containing events, such as when a System Value is changed. In that article, I show a method that uses a combination of two commands, Create Duplicate Object (CRTDUPOBJ) and Display Journal (DSPJRN). The information extracted is all the events in which a System Value was changed. The CRTDUPOBJ command is used to create a usable copy of the IBM-supplied model file for the SV Type of Journal Entries. Once the usable copy of the IBM model file is created with CRTDUPOBJ, the command DSPJRN is used to extract the SV journal entries from QAUDJRN and place them into our copy of the IBM model output file, thereby letting us use simple query tools or download to Excel to evaluate the System Value Change events. There IS Another, and Possibly Better, WayWhile this is one way to extract the data and place it into a usable format, IBM has also provided an alternative method, which you might choose over the two-step method I use in the Feature Article. In release V5R4, IBM introduced the CL command Copy Audit Journal Entries (CPYAUDJRNE). The command, in effect, replaces the older Display Audit Journal Entries (DSPAUDJRNE) command, which only let you print a list of the QAUDJRN journal entries; and the printed list is often missing key data elements from the journal entry. CPYAUDJRNE helps you extract data from the system audit journal (QAUDJRN) and place that data into an entry-specific output file. It would be nice if the new command had the same filtering capability as the more capable DSPJRN command. It lets you filter only by journal entry type, user, journal receivers or from-date/time to-date/time. The DSPJRN command allows additional selection criteria over CPYAUDJRNE, such as Program name and Job that caused the System Value change. However, if you do not need that extra filtering, I recommend using CPYAUDJRNE over DSPJRN. The output file(s) created by the CPYAUDJRNE command is journal-entry–type specific, so you end up with the same result as explained in my Feature article that uses the two-step approach. Here's an example of using CPYAUDJRNE to extract the SV (System Value Change) entries for the date and time period specified in the command.
CPYAUDJRNE ENTTYP(SV) OUTFILE(MYAUDIT/A0512)
JRNRCV(*CURCHAIN)
FROMTIME('05/19/2012' '04:00:00')
TOTIME('05/20/2012' '04:00:00')
This command creates an output file named A0512SV, which contains the SV entries for the time period. You can then use IBM's Query or another query tool to present the data the way you want it. For example, to list all the System Value Changes for that time period, you could use the command: RUNQRY QRYFILE((SECURITY/A0%12SV)) You can review The 6.1 CPYAUDJRNE command documentation here. |
Sponsored Links
IBM i, iSeries and AS/400
|
|
|
||
|
||
|
Send your IBM i Security Related News and Events! Sponsor the SecureMyi.com Security Newsletter © Copyright 2012 - SecureMyi.com, all rights reserved SecureMyi.com | St Louis MO 63017 |
||