|
||
|
SecureMyi.com Security and Systems Management Newsletter for the IBM i
February 26, 2014 - Vol 4, Issue 3
|
||

|
||

|
Feature Article
|
|
In This Issue
Quick Links
Our Newsletter Sponsors
Platinum Sponsor |
IBM i Security ResourcesIBM i Security Videos - SecureMyi RedBook - Security Guide IBM i 


|
|

|
||
|

|
|
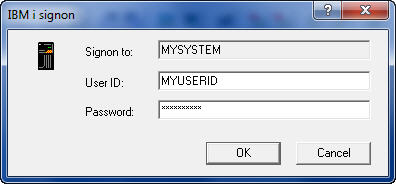
Security Shorts - Using QPWDRQDDIF with QPWDCHGBLK
By Dan Riehl The System Value QPWDRQDDIF has been available for many years as a means of forcing users to choose new or previously 'unused' passwords when changing their password. The number you specify for the System Value determines 'How many previous passwords are checked' to ensure that the new password has not been used, or not been used recently. The number specified in the System Value corresponds to the number of previous passwords that are checked. Value Specified Number of previous passwords checked 0 0 � No Previous passwords are checked, Can be the same 1 32 2 24 3 18 4 12 5 10 6 8 7 6 8 4 I always wonder at "technology" like that exhibited in this System Value. Why not just allow me to specify the number of previous passwords to check, instead of a number that corresponds to a number of previous passwords to check? If I want to check the previous 6 passwords, I specify the number 7 for the System Value QPWDRQDDIF. Who thought this up? What if I want to check for the previous 5 passwords? It can't be done. hmmm. In IBM i 6.1, IBM provided an additional system value that allows you to more strictly enforce the 'password difference' rule. The new system value is QPWDCHGBLK(Block Password Changes), which allows you to specify a number of hours in which a newly changed password cannot be changed again. A password change is temporarily blocked. The shipped value is *NONE, which means that a newly changed password can be changed again immediately. That is also the behavior we have prior to 6.1. And that is where our users have taken advantage of the lack of a password change blocking mechanism. Prior to 6.1, users can repeatedly change their password until they have exhausted your Password Difference System Value. Their goal, and the ultimate result is that they have been able to reset their password back to the same password that they have used for years. It's so much easier to remember, Ya Know? The QPWDCHGBLK System Value allows you to enforce a timer which says 'You cannot change your password again for n number of hours'; where n is a number from 1 to 99. So, once a user has successfully changed their password, they are prohibited from changing their password again for the number of hours that you specify in the System Value. For added security, a security administrator can always change a user's password using the CHGUSRPRF(Change User Profile) command. On another note; the password change block is not in effect when the user's password has been 'Set to Expired' using CHGUSRPRF. The Password Change Block System Value can be overridden at the User Profile level using the PWDCHGBLK parameter of the CRTUSRPRF and CHGUSRPRF commands as shown here: CRT/CHGUSRPRF USRPRF(MYUSER) PWDCHGBLK(*SYSVAL, or a number 1-99) |
Sponsored Links
IBM i, iSeries and AS/400
|
|

|
||

|
||
|
Send your IBM i Security and Systems Management News and Events! Send your Questions, Comments, Tips and Stories Copyright 2014 - SecureMyi.com, all rights reserved SecureMyi.com | St Louis MO 63017 |
||