|
||
|
March 14, 2012 - Vol 2, Issue 6 |
||
|
||

|
Carsten's Security Code for IBM i
Managing the Online Retention of Audit DataDownloadable Source code included!
By Carsten Flensburg When you decide to begin auditing security related events on your system to the QAUDJRN journal, or when you start journaling changes to physical files, data areas or data queues, you must also decide how you are going to manage the online retention of the journal's receivers. The journal receivers are the storage areas used for the audit records generated by system auditing or database journaling. If left unchecked, these journal receivers will continue to expand in size and number, and may ultimately consume all of your available disk space. When you want to control how long journal receivers are available online, you will want to "age" the receivers. For example, if you want to keep five days' worth of transactions online, you can either manually delete the old receivers or run the RMVJRNRCV(Remove Journal Receivers) command presented here. The Remove Journal Receivers (RMVJRNRCV) command lets you age the receivers and optionally connect the journal to a new receiver. You can run this command from a command line, or better yet, place the command in your job scheduler to ensure daily or weekly "Aging" of your journal receivers. You can use this command to manage all of your journals, including QAUDJRN and database journals to perform an intelligent deletion of old receivers. |
|
In This Issue
Carsten's Security Code for IBM i Security Quick Links
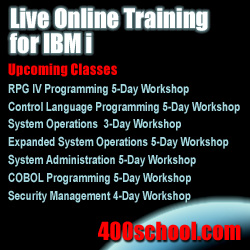
SecureMyi Website Please Visit Our Sponsors
Platinum Sponsor |
IBM i Security and Audit ResourcesIBM i Security Videos from SecureMyi.com SecureMyi Newsletter Home and ArchivesIBM i Security Reference - IBM i 6.1 IBM i Security Reference - IBM i 7.1 QAUDJRN Audit Types By AUDLVL 6.1 QAUDJRN Entry Type Record Layouts 6.1 PCI SSC Data Security Standards 


|


|
Featured YouTube VideoIBM i Security - Function Usage - The Secret Security Options

Cannot Access Youtube from your office? Here is the presentation in wmv format. |
||
IBM i Security Calendar of Events
|
|
|
|
||
Security Shorts

Registered Exit Programs
By Dan Riehl Have you ever used the WRKREGINF command? It is the IBM i command to Work with Registration Information. So, you ask, "What is Registration Information anyway?" Simply put, it is the registered exit points and exit programs that allow IBM, third party vendors and you to do some custom processing when an event occurs on your system. For example, IBM provides a registered exit point for the process of creating a user profile. It allows you to do some custom programming when a user profile is created. You accomplish your custom processing by writing a program, and registering the program using the WRKREGINF command or the ADDEXITPGM(Add Exit Program) command. There are many categories of exit points. Some are for Backup and Recovery, User Profile maintenance, Network Access(Like FTP and ODBC), and many others. Thankfully, the ability to add an exit program to the registry is restricted to a user with Security Officer access. I say thankfully, because it is possible through adding exit programs to override the normal functioning of the system. That’s what the exit points were designed for. Now, please let me take you a step further . . .Several releases ago, IBM provided us with the capability to add exit programs to Control Language commands. These are referred to as Command Exit programs. So, if you wanted to add your own custom logic to a CL command, you could do that through registering your own custom written program to the IBM supplied exit point named QIBM_QCA_CHG_COMMAND. Please, just one more step with me . . .When installing third party vendor supplied packages you are often required to log-on to the system as QSECOFR, or similar powerful user profile. This, in itself, is not a bad thing. But, do you know what the vendor's install process is doing to your system? I was recently at a customer site performing a security assessment and was running a standard audit report from my bag of tricks and discovered a little surprise deposited by a third party vendor’s install process. The vendor had added an exit program for the IBM supplied Control Language command APYPTF(Apply Program Temporary Fix). I was puzzled. Why would a well-respected software vendor want to hook their own logic into the PTF process, especially when the software product itself had absolutely NO relationship to system fixes or PTFs? I questioned the vendor about what this exit program was doing there. The vendor did not provide any kind of reasonable answer, and advised me that it was ok to remove the exit program if I wanted to, it would not affect their application. So why was it there in the first place? Hmmmm . . . You can review all the exit programs on your system by using the WRKREGINF command, and paging through all the screens, or you can print a report using the same command. You will find that the printed report is a bit complex, but look for exit programs, especially Non-IBM supplied exit programs. In an upcoming issue of the newsletter we will provide the source code for a command that will provide a better list of registered exit programs. So What Do I Do Now?I want to suggest something that may increase your comfort level when installing new software. Start the IBM i auditing function for the user doing the install, to include auditing command execution and system changes. When the install is complete, run some auditing reports to determine what happened during the install process. Here’s a command to start auditing a user’s actions before you start the install process. (Note: If you are auditing some of these at the system level(i.e. in the QAUDLVL system value, you do not need to include them at the User level. But you will want to include at least *CMD, since that cannot be specified at the system level. It will provide an audit trail of every CL command executed by that user. CHGUSRAUD USRPRF(MYUSER) +
AUDLVL(*CMD *CREATE *SYSMGT *SERVICE *SAVRST *SECURITY *OBJMGT)
|
Sponsored Links
IBM i, iSeries and AS/400
|
|
|
||
|
||
|
Send your IBM i Security Related News and Events! Sponsor the SecureMyi.com Security Newsletter © Copyright 2012 - SecureMyi.com, all rights reserved SecureMyi.com | St Louis MO 63017 |
||