|
||
|
March 28, 2012 - Vol 2, Issue 7 |
||
|
||

|

A Tale of Leaky Data - Spooled Files
By Dan Riehl A "data leak" is defined in Wikipedia as "the intentional or unintentional release of secure information to an untrusted environment." It can also be called a "data spill" or "data breach." We are often deeply concerned about data leaking from our production database to the outside world. We often focus a great deal of effort on securing these precious data jewels we call files. But what about protecting the end result of these jewels�our printed reports? Our production reports consist of our precious data jewels, coordinated, manipulated, and cajoled into what becomes meaningful information in the form of a production report. If we consider our database files to be sensitive, then our printed reports, which present that file data in a readable, organized format, must be protected with as much or, dare I say, more due diligence. If your shop is like most, all, or almost all, output queues are left unsecured. For some strange reason, we assign *JOBCTL special authority to our end users. The result of this *JOBCTL assignment is that they can view and manipulate the reports generated by others. This is usually the root of the problem of data leakage via printed reports. A user with *JOBCTL special authority can, with few exceptions, view and control any printed report on the system. Perhaps to avoid the potential of a data leak through a printed report, we configure the user accounts with the command line restriction LMTCPB(*YES). As a further step, we don't present a menu option that allows them to view the spooled files of others. That's a nice solution, but there still can be alternative methods to view and leak the data in our sensitive reports. One such method is through the IBM i Navigator for Windows (a.k.a. Operations Navigator) Basic Operations tab. |
|
In This Issue
Tale of Leaking Data Security Quick Links
Please Visit Our Sponsors
Platinum Sponsor |
IBM i Security and Audit ResourcesIBM i Security Videos from SecureMyi.com SecureMyi Newsletter Home and ArchivesIBM i Security Reference - IBM i 6.1 IBM i Security Reference - IBM i 7.1 QAUDJRN Audit Types By AUDLVL 6.1 QAUDJRN Entry Type Record Layout 6.1 RedBook - Security Guide for IBM i 6.1 PCI SSC Data Security Standards 


|


|

Featured YouTube Educational VideoIBM i Security

Cannot Access YouTube from your office? Download the video in wmv format. |
||
IBM i Security News Bytes
Great New Book Arrives - IBM i Security Administration and Compliance
IBM Introduces Quick Security Check for IBM i
ProData Computer Services Inc, Releases RDR 4.0, Retrieve Deleted Records.
Do More With Less: CCSS Issues a Cheat Sheet for IBM i Managers IBM i Security Calendar of Events
|

|
|
|
||
Security Shorts

Protecting Sensitive Data � But - Where is it?By Dan Riehl When we discuss the security and protection of sensitive data like credit card numbers, Bank Account Numbers and Social security Numbers we tend to focus solely on our storage of this information in our DB2 database. We perhaps use field level encryption, and set the library and file level security to allow only sanctioned users to view or change this data as it is stored in our production files. But, the database file is NOT the only place where this sensitive information can be compromised. Here's a short list of other places where sensitive data might be compromised. I'm sure you can add some instances to my list. Test versions of FilesYes, we all have versions of the production files in our test, development and QA environment libraries. Unless we are using scrubber software for creating these "Test" versions, all sensitive data is available to anyone with access to these files, and copies of these files. Sadly, very few of us use any such scrubber tools. Test data must be sanitized to make sure that all sensitive fields are changed to hide the actual sensitive data. I have not heard of any commercial data scrubbers available specifically for DB2 on i. If you know of any, please let me know. Backup FilesOften backup files are created using command like CPYF CRTDUPOBJ CPYLIB. These versions, if created, must be protected as diligently as the production data it was copied from. In most commercial High Availability solutions, we typically have an exact duplicate of production files on our backup system. But, often we have less strict controls over user access on the backup system. Data on the backup Systems must be protected. Backup MediaOur backup tapes and save files contain all production data. If a backup tape can be restored on to a different system, all files may be compromised. A save file containing production data may be moved to a different system using FTP or any file transfer facility. We must control the ability to save database files to save files, and to transfer data between systems. We also need to exercise strict control over our backup media. Reports in Output queuesPrinted reports often contain sensitive data. While we strive to protect the database, we often overlook the exposure of listing that same sensitive data within spooled file reports. The sensitive data is exposed to users that can view spooled file reports. Just recently, I was working with a customer to secure their sensitive data, and we found it was painfully easy for users to view the payroll register reports while these reports were sitting on an unprotected output queue. The Name, Social Security Number, Pay Amount, Deductions, etc were listed in plain sight for any user to view. IFS spreadsheets, PDF and text filesWe often store spreadsheets and pdf reports in the Integrated File System. Don't forget to secure the sensitive data that resides there. Data in transit, FTP, File Transfer, DRDA, DDM, ODBC, etcUsers who are authorized to their application data, and powerful IT users can usually transfer files using tools like FTP and IBM I Access for Windows File Transfer Facility. These types of transfers must be controlled, and audited and reported. Network Exit Point programs for FTP, DDM and ODBC are required in order to have visibility and control over these file transfer events. |
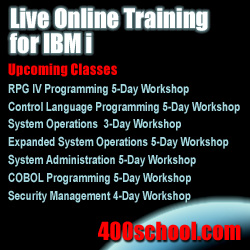
Sponsored Links
IBM i, iSeries and AS/400
|
|
|
||
|
||
|
Send your IBM i Security Related News and Events! Sponsor the SecureMyi.com Security Newsletter © Copyright 2012 - SecureMyi.com, all rights reserved SecureMyi.com | St Louis MO 63017 |
||